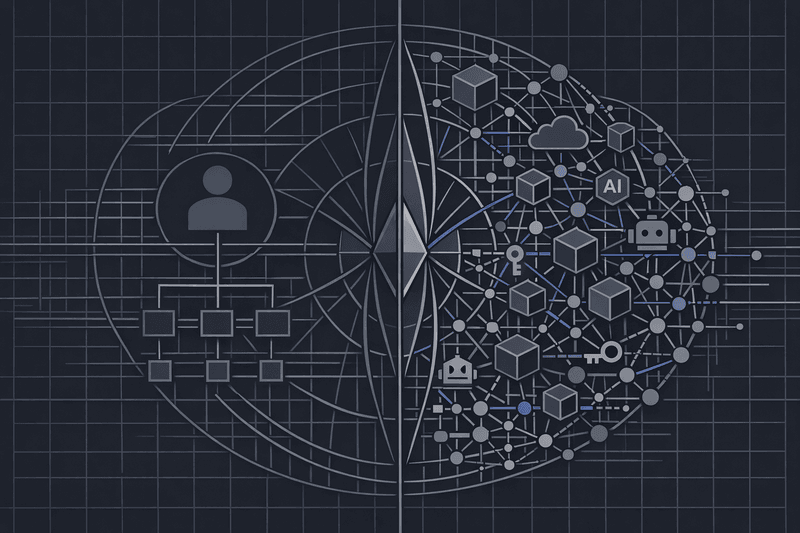
Non-human identities-service accounts, API keys, bots, RPA scripts, CI/CD pipelines, and now AI agents-are now the dominant "workforce" in most environments.
Recent studies estimate non-human identities outnumber humans by 20:1 to over 80:1, with some cloud-native environments exceeding 100:1. That's thousands of always-on credentials, often with privileged access and minimal governance.
In 2026, this becomes not just a security issue but a regulatory one.
- EU AI Act: High-risk AI systems require strict logging, transparency, and technical controls.
- NIST CSF 2.0: Identity management for "users, services, and hardware" is now mandatory.
- ISO 27001:2022: Service and privileged accounts must have owners, least privilege, and reviews.
- NIS2: Identity and access management are baseline requirements with board-level liability.
The EU AI Act entered into force on 1 August 2024. Most obligations phase in over 6-36 months; fines can reach up to 7% of global annual turnover for serious violations. NIST released Cybersecurity Framework 2.0 on 26 February 2024, adding a Govern function and explicit requirements for all identities and credentials. ISO 27001:2022 Annex A controls (A.5.16, A.8.2) require service and privileged accounts to have ownership and periodic review. NIS2 Directive (EU) 2022/2555 must be transposed by 17 October 2024, and German guidance expects Article 21 technical evidence by April 2026 for many SaaS providers.
If your stack still assumes "identity = humans in SSO," regulators now expect you to close those blindspots.
This article compares two approaches:
- Traditional human-centric identity management-SSO plus manual processes and partial tools.
- Unified non-human identity governance-a complete IGA model covering humans, AI agents, and service accounts together (Iden's approach).
We compare both through a 2026 regulatory lens and close with actionable recommendations.
Summary: Traditional vs Unified Non-Human Identity Governance
| Criteria | Traditional human-centric identity management (SSO + manual + partial tools) | Unified non-human identity governance (Iden-style) |
|---|---|---|
| Identity scope | Focused on workforce users in SSO/HR; non-human identities scattered and unmanaged | Humans, AI agents, service accounts, API keys, workloads all governed together |
| App coverage | Strong for SSO/SCIM apps; long-tail, legacy, and custom apps mostly manual | Universal-across SCIM, API, and no-API apps; one place for all identities/app governance |
| Regulatory alignment | Controls focus on human access; hard to prove governance for AI agents and service accounts | Maps controls to every identity; continuous access governance and documentation |
| Audit evidence | Spreadsheets, tickets, ad-hoc exports-audit prep is manual and heavy | Immutable audit logs, automated reviews, real-time reports-all identities/apps |
| Non-human identity scale | Manual tracking/reviews break at scale; orphans and zombie accounts accumulate | Discovery, lifecycle automation, agentic (AI-driven) workflows handle identity sprawl |
| Ops overhead | Mix of SSO, custom scripts, point tools-brittle, high-touch | Plug-and-play connectors, policy-driven, zero engineering overhead, built for lean teams |
| Cost | Rising SaaS tiers, identity tool sprawl, SCIM tax | No SCIM tax, automatic license reclamation, unified evidence for all frameworks |
Option 1: Traditional, Human-Centric Identity Management
Most fast-growing companies didn't design for AI agents or service accounts. Their stack typically includes:
- SSO (Okta, Entra ID, etc.) for workforce authentication
- Lifecycle automation for SCIM apps
- Manual provisioning elsewhere-long-tail SaaS, legacy, internal tools
- Service accounts tracked (if at all) in password vaults, wikis, or notes
- Quarterly access reviews in spreadsheets
Strengths:
- Better than app-by-app passwords
- Familiar to auditors-SSO + manual reviews is expected
- Easy startup-most orgs use this today
Weaknesses:
- Non-human identities everywhere-CI/CD, bots, API tokens, AI agents
- Fuzzy ownership-who owns that old service account?
- Manual, episodic reviews-auditors see rubber-stamp approvals, not real decisions
- Only part of app estate is automated-the rest relies on memory
This model is unsuited for a world where one team can generate thousands of API keys and AI agents in a quarter.
Option 2: Unified Non-Human Identity Governance (Iden-Style)
The solution is one identity fabric-govern humans and machines equally and continuously.
Iden embodies this approach:
- Single platform for all users, agents, service accounts, and contractors
- Universal connectors to any app-no required SCIM or forced enterprise-tier upgrade
- Fine-grained control across channels, repos, projects, environments
- Agentic workflows-AI-driven, autonomous provisioning and right-sizing of access
- Immutable audit logs; continuous reviews
Iden customers report around 80% fewer manual access tickets, save roughly 120 hours per quarter on reviews, and up to 30% lower SaaS spend through license reclamation and avoiding unnecessary upgrades.
This is not UI polish on legacy IGA-it's a new starting point: every identity, human or machine, is governed the same way.
Head-to-Head: Critical Criteria
1. Identity Coverage: Humans vs Non-Humans
Traditional:
- Identities modeled as users from HRIS/AD; non-human identities created outside central processes, often shared, with unclear lifecycle
- Service accounts listed in password vaults without context
Unified:
- Every authenticatable principal is an identity-human, workload, bot, AI agent
- Central catalog includes type, owner, business purpose, permissions
- AI-driven discovery surfaces "identity dark matter": orphaned, stale, unused credentials
2026 Context: NIST CSF 2.0 and ISO 27001 demand identity-level answers for AI agents and service accounts. If you can't answer "who can do what" for non-humans, you're already offside.
2. Regulatory Alignment
EU AI Act
AI Act phases in obligations through 2026/2027 for high-risk systems-risk management, logging, technical documentation.
Traditional:
- Controls who can access AI platform UI-not the agents themselves
- Audit trails often disconnected from agent identities
Unified:
- Models each AI agent as a unique, governed non-human identity
- Policies, time-bound access, audit trails for all agent actions
- Full traceability and accountability, as required by the Act
NIST CSF 2.0
NIST CSF 2.0 covers identity and access for users, services, and hardware across the lifecycle.
Traditional:
- Solid for humans (provisioning, SSO, MFA)
- Weak for non-humans-service accounts often bypass workflows, static credentials, little monitoring
Unified:
- Lifecycle automation for all identities, human or machine
- Policies and continuous monitoring across the full estate
- Easier CSF compliance-central proof, less chaos
ISO 27001:2022
ISO Annex A 5.16/8.2 require owners, justification, least privilege, and review for all accounts-including service accounts.
Traditional:
- Human accounts usually compliant; non-human rarely are-shared, stale accounts, poor logging, evidence spread across exports
Unified:
- Owners and justifications required for every identity
- Automated reviews, mapped to ISO controls, with clear audit evidence
NIS2
NIS2 enforces board-level accountability, technical/organizational measures (Article 21), and heavy fines (at least €10M or 2% revenue).
Traditional:
- Can prove human SSO/MFA, but struggles with complete, live inventory of privileged/technical accounts and their governance
Unified:
- Consistent, testable policies for all identities
- Live evidence-immutable logs, attestation records-for rapid audit response
3. Evidence and Auditability: Static vs Continuous Proof
By 2026, "documentation only" won't satisfy auditors-they want live evidence.
Traditional:
- Evidence gathering = project: pull lists, merge spreadsheets, chase approvals, export tickets
- Static checks vs continuous attacks-misses evolving risk
Unified:
- Immutable logs; real-time access decisions
- Reviews are scoped and actionable-see purpose, usage, and revoke or extend in one click
- Auditors view live system, not stitched-together spreadsheets
This is the difference between security theater and real, testable control.
4. Scale and Automation: 10-100x More Non-Human Identities
Manual processes collapse at scale.
Traditional:
- Each service account is an exception; scripts and approvals turn brittle
- No organizational learning-humans do the heavy lifting
Unified:
- Designed for non-human dominance
- Agentic workflows-automatic discovery, risk classification, access tuning, revocation
- Human teams focus on exceptions-platform covers the long tail
5. Cost, SCIM Tax, and Tool Sprawl
Identity isn't just a compliance issue-it's a budget line.
Traditional:
- Pays the SCIM tax-upgrading apps for SCIM support
- Adds point solutions-PAM, secrets, access reviews, AI governance
- Overlapping licenses and duplicated controls
Unified:
- Automates across any app tier-no SCIM or API required
- Consolidates governance, automation, and compliance evidence
- Recovers spend through license reclamation, avoids forced upgrades
6. Future-Readiness: AI Agents & New Species of Identities
AI agents are here and proliferating-autonomous bots working across your stack.
Traditional:
- Treats agents as "just more integrations"-another API key, shared account
- Governance stops at deployment-not at what the agent is authorized for
Unified:
- AI agents become first-class, governed identities-roles, scopes, behavioral monitoring
- Aligned with EU AI Act, NIST AI RMF, ISO/IEC for machine governance
When regulators ask about AI agent access, you'll need more than "we have SSO."
Recommendations: What Makes Sense for 2026?
When traditional, human-centric might be "enough"
- Small org (<100 employees), minimal automation/AI
- Non-human identities are countable, static, and centrally documented
- Light regulatory scope (no NIS2, no high-risk AI)
- Willing to absorb manual effort every audit
Still, you should:
- Build a register of service accounts with owners/purposes
- Enforce vaulting/rotation for technical accounts
- Quarterly reviews covering all identities
When unified non-human governance is the safer bet
- NIS2 in scope (essential/important entities)
- Developing/deploying high-risk AI systems (EU AI Act)
- Pursuing ISO 27001:2022, already feeling the burden of privileged/service account review
- Moving to NIST CSF 2.0 and need real, comprehensive evidence
- Non-human identities vastly outnumber humans (true for most modern SaaS, cloud orgs)
The question isn't "Do we need non-human governance?"-it's "Can we keep faking it with human-only tools?"
Unified, AI-native IGA platforms like Iden answer that with:
- Complete coverage for all identities and apps (even non-SCIM, no-API)
- Fine-grained control-channel, repo, project-level
- Continuous governance and audit evidence (EU AI Act, NIS2, ISO 27001, SOC 2-and more)
For IT leaders facing real compliance deadlines, it's the difference between fire drills and true readiness.
FAQ
1. Do regulators care about non-human identities?
Yes. NIST CSF 2.0, ISO 27001:2022, and NIS2 all reference "identities, credentials, and privileged access"-not human-only. Guidance increasingly names technical/service accounts. Auditors expect governance of service accounts and agents by default.
2. Is SSO enough for NIS2 or ISO 27001?
No. SSO is necessary, but auditors require:
- full inventory of privileged/technical accounts
- least-privilege and time-bound access
- review evidence (not just logs)
- deprovisioning for all identities, not SSO-only
SSO-only approaches typically miss long-tail SaaS, legacy, and machine access-prime auditor targets.
3. How do AI agents fit identity categories?
AI agents are non-human principals. Governance-wise, they're closer to service accounts/workloads than users. They need:
- unique identity and credentials
- clear ownership and scope
- minimal necessary access
- oversight and monitoring
Treating agents as "just API keys" is tough to justify as regulations mature.
4. Can we bolt non-human governance onto our stack instead of switching platforms?
You can script, but you end up with:
- custom playbooks few understand
- more tools for secrets, agent governance, service accounts
- fragmented logs/evidence, all stitched together before audits
For high-growth, regulated orgs, consolidating into a unified platform is usually faster, simpler, and cheaper long-term.
5. How does this help multi-framework compliance?
Treating all identities consistently, with continuous controls, puts you ahead for:
- SOC 2, CMMC, HIPAA, DORA, and more
Central evidence powers compliance everywhere. That's the ROI of unified non-human identity governance: solve once, prove everywhere.