Here's a scenario that plays out more often than anyone admits: a security incident gets investigated, and the trail leads back to an account still active six months after the person who owned it stopped working for you. Not an employee - a contractor. Someone brought in for a three-month project, did the work, and left. Their Slack access, their GitHub membership, their Figma workspace, their staging environment credentials - all still live. Because nobody revoked it.
That's not a hypothetical. It's the category of finding that triggers audit remediation plans, accelerates vendor conversations, and occasionally ends with a regulatory notice. Almost every time, the root cause is the same: the contractor had standing privileges - permanent, unchecked access that nobody was watching and nobody revoked.
The fix isn't more offboarding checklists. It's a different model of access from day one.
The Problem With "Permanent Until Revoked"
Standing privileges - access rights that remain active indefinitely until someone manually removes them - are the default for most contractor access today. A contractor is onboarded, typically through a ticket or a manager request, gets "the same setup as the dev team," and starts work.
Then the contract ends. And the model breaks.
Contingent workers are prime targets for bad actors precisely because turnover is high and orphaned accounts stack up when there's no defined cleanup process. These users often don't exist in a central repository like an HRIS, making it difficult to identify a status change quickly enough to revoke access in time.
Among organizations that suffered breaches, over 65% lacked automated processes for onboarding and offboarding users. This gap creates orphaned accounts and excessive privileges that attackers exploit.
The arithmetic is brutal. A company with 30 active contractors, each accessing 8-10 apps, cycling through 3-month engagements - that's potentially hundreds of access grants to track, right-size, and revoke across dozens of apps, every quarter. Manually. Contractors and vendors often retain long-lived credentials because revocation gets missed or automated processes aren't configured correctly.
Security researchers found 27% of cloud breaches in 2024 involved misuse of dormant credentials - many tied to orphaned accounts. The standing privilege model creates exactly these conditions: broad access, no expiration, and no one watching.
Why Standing Privileges for Contractors Are a Structural Problem
It's worth being precise about why this keeps happening, because the answer isn't "IT teams are lazy." It's architectural.
Most identity governance programs were built around employees with HR system records. When an employee is terminated, a lifecycle event fires, SSO gets disabled, and (for apps with SCIM) deprovisioning runs. The system works - for employees, for SCIM-enabled apps, during normal business hours.
Contractors break every one of those assumptions:
- No HR record. They exist in a spreadsheet, an email thread, or a vendor management portal - not in the HRIS that triggers your lifecycle automation.
- No standard offboarding event. When a contract ends, IT might hear about it weeks later - if they hear about it at all.
- Broad initial access that never gets reviewed. "Give them what the dev team has for now" is the most common provisioning instruction, and it never gets walked back.
- Accounts outside the SSO perimeter. Contractors are frequently onboarded with personal email addresses to project tools, shared accounts for client portals, or direct credentials to apps where the company isn't paying for SSO-connected seats. Disabling someone in Okta doesn't touch those.
Incredibly, 14% of security leaders say they have "no idea" how many standing privileges remain in their cloud platforms, and 10% of organizations report "no visibility" into privileged access across their multi-cloud environments. For contractors - who are often outside the tracked perimeter entirely - that identity blindspot is even larger.
Standing privileges for contractors aren't a process failure. They're a design failure. The model was built for full-time employees and simply doesn't extend to everyone else who touches your systems.
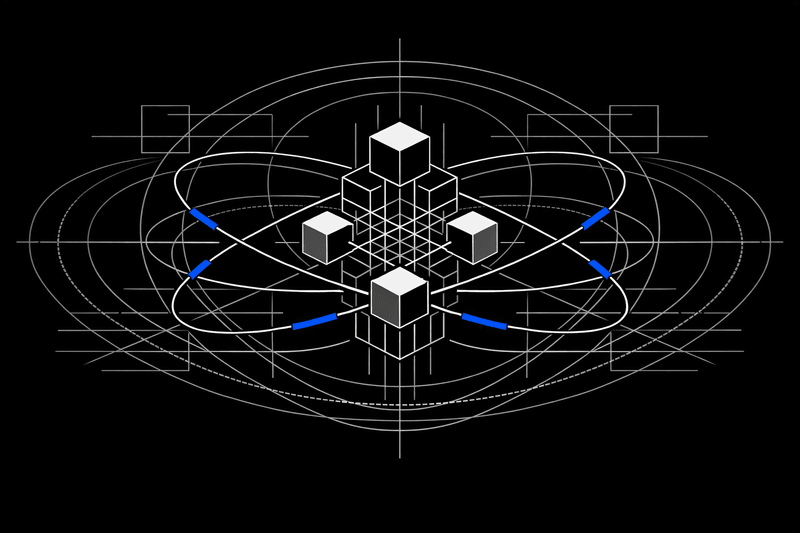
What Time-Bound Access and JIT Provisioning Actually Mean
These terms get used interchangeably, but they describe distinct - and complementary - controls.
Just-in-time (JIT) provisioning means access is created on demand, at the point of need, rather than pre-provisioned and sitting idle. When a user attempts to access a specific application, their account is created or updated dynamically with the necessary permissions. Once the task is complete or a set time expires, access is automatically revoked or deprovisioned. This approach is critical for contractors, temporary staff, and project-based roles - ensuring they have access only for the required period.
Time-bound access means every access grant has a hard expiration - a date or condition at which access ends automatically, without requiring anyone to remember to do anything. The access self-destructs on schedule.
For contractors, the right model combines both:
- Access is provisioned fast at the start of the engagement (JIT - no weeks-long wait for IT tickets)
- It's scoped precisely to what they need (specific repos, channels, or projects - not "the whole team's setup")
- It carries a hard expiration date tied to the contract end or project milestone
- Revocation is automatic, verified, and logged across every app in scope
Implementing just-in-time ephemeral (non-standing) access for all users - both human and service identities - across multiple platforms is a crucial first step.
The contrast with the default model is stark:
| Access Attribute | Standing Privileges (Default Today) | Time-Bound / JIT Access (Best Practice) |
|---|---|---|
| Duration | Permanent - until someone remembers to revoke | Scoped to project, sprint, or specific window |
| Scope | Broad - 'same setup as the dev team' | Fine-grained - specific repos, channels, projects |
| Offboarding trigger | Manual ticket (or nothing) | Automatic - expires by policy or contract end date |
| Orphaned account risk | High - accounts outlive contracts by months | Minimal - access self-destructs on schedule |
| Audit trail | Fragmented, hard to reconstruct | Complete - every grant and revocation logged |
| Compliance posture | Reactive - discovered at audit time | Continuous - enforced in real time |
| Blast radius if compromised | Wide - attacker inherits all standing permissions | Narrow - limited to scoped, time-bound session |
How Much Is Standing Contractor Access Actually Costing You?
The risk is easy to describe in the abstract. Use the calculator below to see what the numbers actually look like for your organization.
The Coverage Problem Nobody Talks About
Here's the part of the JIT conversation most platforms quietly skip: they can only enforce time-bound access for apps that support SCIM or a full API.
That typically covers 20-40% of the apps a contractor actually touches. The rest - the project management tools, the design platforms, the internal dashboards, the legacy portal where the team manages one specific workflow - get left out. You can set an expiration policy in your IGA platform all you want, but if the platform can't reach the app to revoke access, the policy is just documentation.
The SCIM wall is real - and it's where time-bound access breaks down. Most IGA tools enforce JIT and time-bound access only for apps that support SCIM or a full API. The rest of your stack - Figma, Notion, Linear, your internal project portal, that legacy procurement tool - gets manual processes and wishful thinking. Universal connectors are the only way to enforce ephemeral access across 100% of the apps a contractor touches.
Organizations that haven't enforced JIT access carry significantly higher security risk and make compliance exceedingly complex and time-consuming. Conversely, organizations that implement JIT ephemeral access massively reduce the access entitlements that must be reviewed during certification processes.
But that benefit only materializes if the JIT controls actually reach all the apps - not just the SCIM-friendly ones.
This is the coverage gap that the "modern IGA" category has largely ignored. Platforms built on SCIM-first architecture deliver time-bound access for a fraction of the stack and declare the problem solved. The other 60-80% of applications - the long-tail SaaS, the legacy portals, the tools where enterprise plans weren't purchased because someone was trying to avoid the SCIM tax - remain governed by manual processes and hope.
Universal connectors - ones that work via API, browser-level automation, or proprietary methods where neither exists - are the only mechanism that closes this gap. If the connector can provision access into an app, it can revoke it. If it can set a time-bound scope at provisioning, it can enforce that scope consistently. That's what "complete coverage" actually means in the context of ephemeral access.
Implementing Time-Bound Access for Contractors: The Five-Step Model
Getting from standing privileges to ephemeral access by default isn't a rip-and-replace project. It's a policy and tooling shift that can happen incrementally, starting with the highest-risk apps and contractor populations.
Before a contractor gets a single login, define exactly what they need: which apps, which resources within those apps (repos, channels, projects), and for how long. This is not 'same setup as the dev team' - it's the minimum viable access for the engagement. Store these parameters in your governance policy, not in someone's head.
A calendar reminder to 'check if contractor is still active' is not a control. It's a bet. Set a hard expiration on the access itself - tied to contract end date, project milestone, or a defined window. When the date hits, access revokes automatically, across every app in scope. No ticket required.
Most tools handle time-bound access for SCIM-enabled apps and stop there. But contractors touch Figma, Notion, Linear, internal dashboards, and production environments that don't offer SCIM. Universal connectors - ones that work via API, browser automation, or neither - are the only way to enforce time-bound access across the entire stack, not just the easy 20%.
After the access window expires, verify that revocation actually happened - in each target app, not just in the identity provider. Run continuous reconciliation that compares what the governance layer says should be active against what's actually live in each application. Any mismatch is an alert, not a surprise at your next audit.
Every grant, every scope change, and every revocation should produce an immutable log entry: who approved it, when it was granted, what was included, and when it expired. This isn't overhead - it's the evidence package that answers your auditor's question ('who had access to X between these dates?') in seconds, not weeks.
What Fine-Grained Control Actually Looks Like in Practice
Time-bound access without fine-grained scope is still a problem. Granting a contractor time-limited access to "GitHub" is meaningfully different from granting them time-limited access to the specific repository they need for their engagement.
The distinction matters because:
- Blast radius. If a contractor's credentials are compromised during their active engagement, broad access means an attacker inherits broad access. Repository-level, channel-level, or project-level scoping limits what's reachable.
- Audit defensibility. When your auditor asks "what did this contractor have access to?" - "GitHub" is not a useful answer. "These three repositories, for this window, approved by this person" is.
- SoD compliance. Some access combinations are inherently incompatible - a contractor who can push to production and approve their own pull requests, for example. Fine-grained control enables SoD checks at provisioning time, not as an afterthought during the next access review.
Iden's connectors operate at this level across the stack - down to specific channels in Slack, individual repositories in GitHub, projects in Notion and Figma, and environments in cloud platforms. That's the difference between access governance and access management: governance means you're making decisions, not just assignments.
The Compliance Angle: What Auditors Are Actually Asking
Regulatory frameworks including GDPR, HIPAA, PCI DSS, and SOX all emphasize the principle of least privilege. JIT access provides a natural mechanism to enforce and demonstrate compliance with these requirements through continuous enforcement of minimum necessary access, detailed audit trails of access requests, approvals, and usage, and time-limited authorizations that prevent access sprawl.
When a SOC 2 or ISO 27001 auditor asks about contractor access management, they're not asking whether you have an offboarding policy. They're asking:
- Can you prove who had access to sensitive systems at a specific point in time?
- Can you show that access was scoped appropriately for the role?
- Can you demonstrate that access was revoked when it was no longer needed?
Manual processes produce inconsistent answers to all three. An orphaned contractor account still active three months after contract end is a formal finding, not an "oops." And the remediation typically isn't one finding - it's a program-level gap that triggers a broader controls review.
Time-bound access, enforced through automated governance with immutable audit logs, turns those questions from anxiety-inducing to answerable in seconds. Every grant, scope change, and revocation is logged. The evidence package is always current. And because access expires by policy rather than by memory, there are no orphaned accounts to explain away.
For teams navigating DORA enforcement, NIS2 compliance, or annual SOC 2 reviews with a small IT function, this isn't just a security improvement - it's the difference between answering auditor questions yourself and spending three weeks reconstructing access history from spreadsheets, screenshots, and Slack messages.
Three Contractor Access Scenarios Where This Matters Most
1. The Developer Engagement
A software contractor is brought in for a two-month sprint. They need access to three GitHub repositories, a staging environment, a project board in Linear, and the team's Slack workspace - but only specific channels.
Default model: Give them developer-level GitHub access, add them to all Linear projects, invite them to Slack. Hope someone files a ticket when they wrap up.
Time-bound model: Provision access to the specific repos, the one project in Linear, and the relevant Slack channels. Set a 60-day expiration. When it expires, all of it revokes automatically - including the Slack channels and the Linear project, which don't support SCIM but are reachable via universal connectors.
2. The Healthcare Provider Portal
An external provider needs access to a patient data portal to collaborate on care plans for a defined period. Standing access here isn't just a security risk - it's a HIPAA compliance issue.
Time-bound model: Grant access for the duration of the care episode, scoped to the relevant patient records or case types. When the clinical relationship ends, access expires. No manual revocation required, full audit trail maintained.
3. The Manufacturing M&A Integration
Post-acquisition, a team of external consultants needs temporary access to integrate systems. They'll touch ERP environments, legacy operational tools, and document management platforms - many without SCIM support.
Time-bound model: Provision across the full integration scope using universal connectors. Set a project-end expiration. When the integration is complete and the consultants leave, access across all systems - including the legacy environments - revokes on schedule. No residual access, no orphaned accounts, no audit findings six months later.
Takeaways
Contractor access is not an edge case. Contingent workers make up roughly 30-40% of the U.S. workforce, and that share is growing. Identity governance programs built for full-time employees with HRIS records simply don't extend to these workers - and the standing privileges they accumulate represent a persistent, expanding attack surface.
The fix is architectural, not procedural:
- Ephemeral by default. Contractor access should never be permanent. Every grant should carry a hard expiration tied to the engagement or project.
- Scoped to the need. Not "the dev team's setup" - the specific repos, channels, and projects this contractor actually requires.
- Automated revocation, not reminders. Access that expires by policy doesn't rely on anyone remembering to file a ticket.
- Enforcement across the full stack. Time-bound access controls only work if they reach every app the contractor touches - including the tools without SCIM support.
JIT access minimizes insider threat risk by limiting both the time and scope of access. Even trusted employees or contractors can pose a risk, and JIT access directly mitigates this.
The tools to do this exist. The question is whether your governance platform can actually reach the full stack - or whether it's enforcing ephemeral access for 30% of your apps and leaving the other 70% to chance.
What is the difference between time-bound access and just-in-time (JIT) provisioning?
They're related but distinct. Time-bound access means setting a hard expiration on any access grant - it's active for a defined window and revoked automatically when that window closes, regardless of whether the user logs in or not. Just-in-time (JIT) provisioning means access is created on demand, typically when a user authenticates and needs it, rather than being pre-provisioned and sitting idle. For contractors, you want both: access created quickly when the engagement starts (JIT), scoped tightly to what they need, with a hard expiration when the engagement ends (time-bound). Neither alone is enough.
Why doesn't disabling a contractor in Okta or Entra solve the problem?
Disabling a contractor in your SSO provider removes their SSO-based authentication for apps connected to that provider. But many contractor accounts were never in your directory to begin with - they were onboarded with a personal email, a shared account, or a direct login that bypasses SSO entirely. And even for apps that are SSO-connected, some allow direct authentication as a fallback. The only complete solution is governance that enforces revocation at the application layer, not just at the identity provider.
Do time-bound access controls work for apps without SCIM support?
With the right tooling, yes. Legacy IGA and most 'modern IGA' platforms can only enforce time-bound access for SCIM-enabled apps - which typically covers 20-40% of the apps in a typical SaaS-heavy stack. Universal connectors that work via API, browser-level automation, or proprietary methods can extend time-bound access enforcement to the full stack, including Figma, Notion, Linear, legacy portals, and internal tools. If your platform can't reach an app to provision access, it also can't reach it to revoke access when the time window closes.
What counts as 'standing privilege' for a contractor?
Any access that remains active beyond the explicit need that justified it. If a contractor's GitHub membership, Slack workspace access, Notion workspace, or production environment credentials are still live one day after their contract ends, those are standing privileges. More subtly: access granted at the start of an engagement that was never right-sized or reviewed during the project is also effectively standing privilege - broad, unchecked, and unlikely to be cleaned up properly at the end.
How does JIT access affect the contractor experience?
Done right, it's largely invisible to the contractor. Access is provisioned quickly when the engagement starts, they have what they need to do the work, and it's removed cleanly at the end. The friction points most contractors experience today - waiting days for access tickets to be fulfilled, not having access to the right tools, or being locked out inconsistently - are actually caused by manual provisioning, not by JIT. Automated, policy-driven JIT provisioning is typically faster and more consistent than the manual ticket-based alternative.